3 Security Vendors Getting Messaging Right (And What You Can Learn)
Analysis of how top security vendors convert buyers with messaging. Real examples of what works, what doesn't, and why.
Most security vendors ship messaging that works for engineers. Not for buyers.
I spent the last week analyzing messaging from 20 security companies. Three of them stood out because they do something different. They lead with business impact first, back it up with technical proof second.
That's backwards from how most security vendors think. But it's why these three close deals faster.
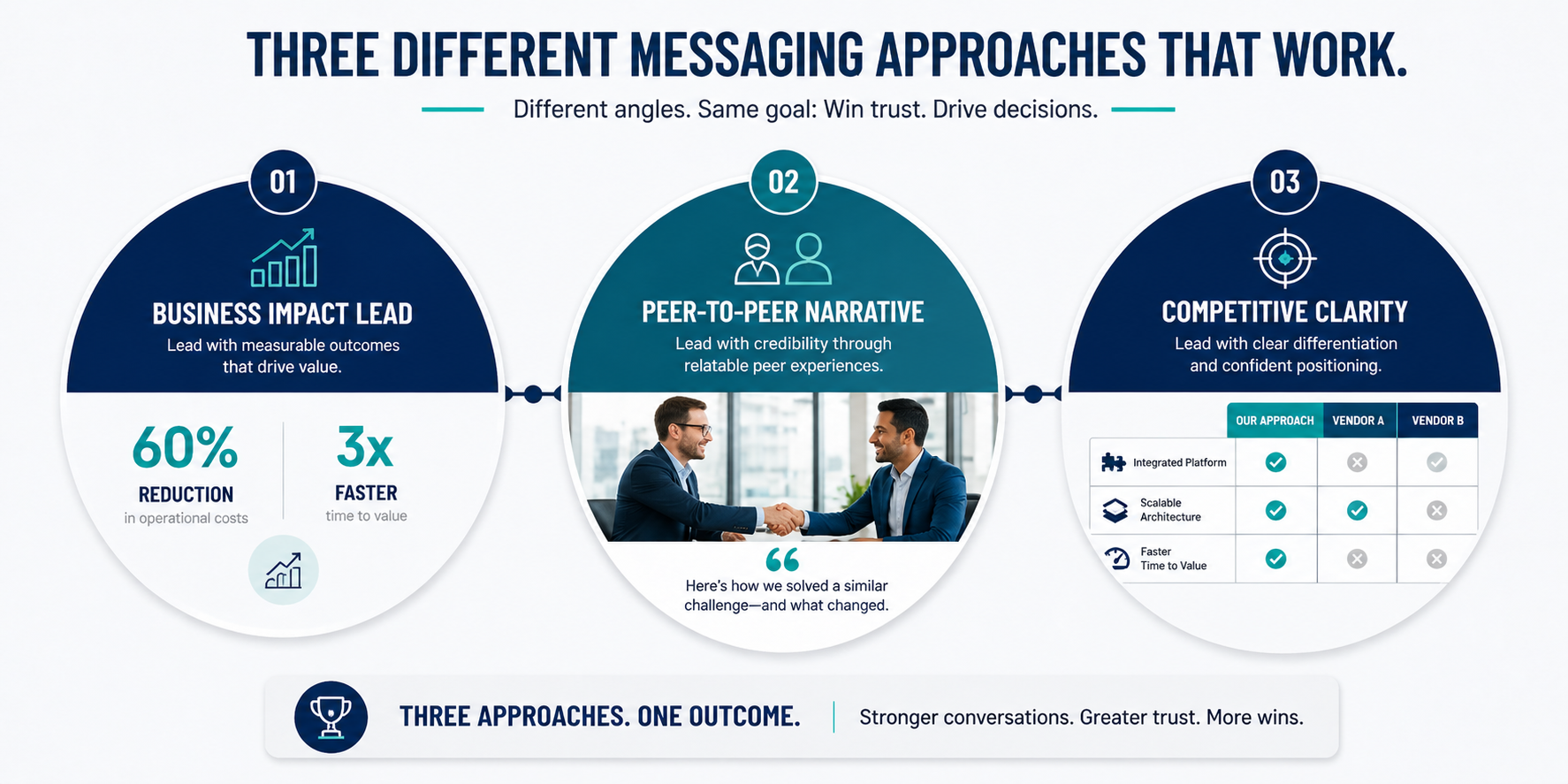
Vendor #1: The Business Impact Lead
This vendor sells a detection engineering platform. Their homepage doesn't start with architecture. Doesn't start with features. Starts with this.
"Reduce alert noise by 60%. Close security gaps 3x faster."
That's it. Two sentences. Business outcome. No technical jargon.
Then they prove it. Case study showing a SOC team that went from 10,000 alerts per day to 4,000. Dwell time dropped from 8 days to 3 days. Cost per incident investigation dropped 40%.
Then—only then—do they explain how. Detection engineering framework. Automated response. Integration pipeline.
Why does this work?
A security buyer opening that page doesn't think "tell me about your architecture." They think "can this solve my problem?" This vendor answered the second question first.
By the time a reader gets to the technical explanation, they already want the solution. Technical detail becomes proof, not confusion.
Vendor #2: The Peer-to-Peer Narrative
This vendor sells a cloud security platform. Their messaging doesn't sound like a vendor.
"We spent three years in the SOC. We saw the same problem repeat: teams securing cloud infrastructure like it's on-prem. It doesn't work. Cloud security is different."
Then they explain why. Different architecture. Different threat model. Different response playbook.
Then they show how their product solves it.
What's powerful here? They positioned themselves as peers who understand the problem. Not as outsiders selling a solution.
Most security vendors position as "we built a product that fixes X." This vendor positioned as "we lived the problem, built a solution because we had to."
That's a narrative buyers respond to. It builds trust faster.
Vendor #3: The Competitive Clarity
This vendor sells a network detection platform. Most vendors avoid comparisons. This one leans in.
"SIEM platforms are built for compliance. NDR platforms are built for detection. Here's the difference."
Then they show a side-by-side. What each platform does well. What each platform doesn't.
Their product isn't positioned as "better SIEM." Positioned as "different category, different job to be done."
Why does this matter?
When a buyer is confused about what you are, they default to price comparison. When a buyer understands what you are and why you're different, they evaluate on value.
This vendor chose clarity over comparison. That distinction matters.
What These Three Have in Common
I looked at what made these three different from the other 17 I analyzed.
- Business impact first. Technical proof second.
- Peer narrative.
- Clear positioning.
- No buzzwords. No fluff.
They all did one thing consistently: they thought about the buyer's question before the vendor's answer.
A buyer doesn't open your page thinking "tell me about your platform." They open thinking "can this solve my problem?" These three vendors answered that question first.
What Most Vendors Get Wrong
The 17 other vendors I looked at all started the same way.
"We are a [category] platform built for [feature]. Our architecture uses [technical jargon]."
That works if your buyer is an engineer evaluating architecture. It doesn't work if your buyer is a security leader trying to close a gap.
Most security buying committees have three people. A technical evaluator who cares about architecture. A security leader who cares about coverage. A budget holder who cares about impact.
The vendors starting with features? They won over the technical evaluator. Lost the other two.
The vendors starting with impact? They won over all three.
How to Audit Your Own Messaging
Open your website. Your latest white paper. Your product page.
Ask yourself: If someone opened this page, what question are they trying to answer?
If your first answer is "tell me about your product," you're starting wrong.
If your first answer is "can this solve my problem," you're starting right.
Most security vendors answer the first question. The ones winning answer the second.
That's the pattern I'm seeing.
Start a Conversation →